SSH Jump / gateway using two different keys
I have a conundrum that I do not know how to solve.
To illustrate the problem I will use an example.
I have 2 servers on Linux, one of them is a jump host.
If I upload my SSH keys to both servers, everything works. However, I would like to implement additional security. I would like the target server to not have my key, but another key of mine for connections between the jump host and the server. That is, if my personal key is stolen, the intrusion will occur at most on the jump host, but not on other servers.
What do you guys think about such a solution, and is it possible to configure RDM this way?
I'll also upload a simple drawing to illustrate what I mean. 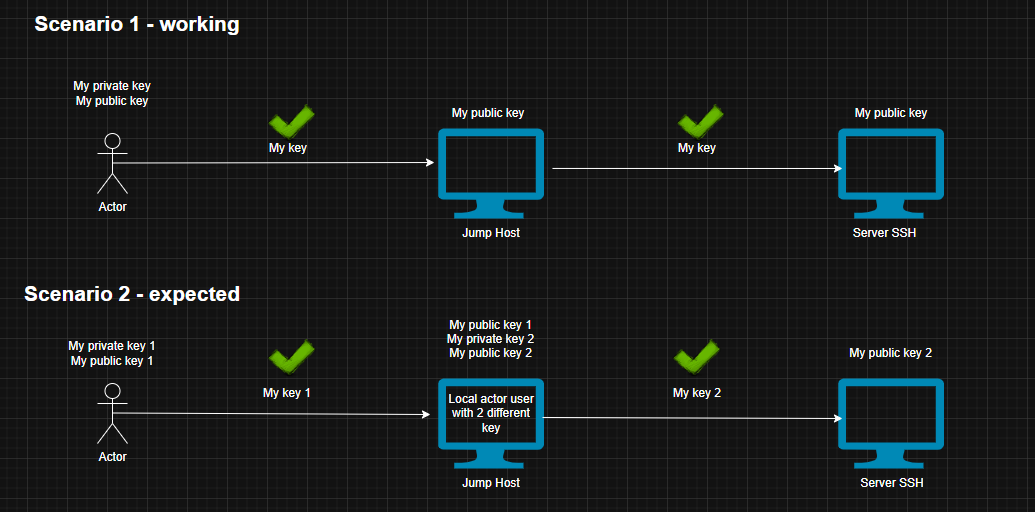
57e782ab-641e-4595-b789-a66559e78749.png
All Comments (1)
Hello,
Thank you for contacting us on this matter
After checking with our dev team, here’s what we can confirm.
RDM already supports using different private keys for the jump host and the target server. The screenshot shows that you can assign a separate key to the SSH gateway connection. Both private keys stay on the client machine. They are not transferred to or stored on the jump host.
This setup is similar to how OpenSSH handles jump hosts. RDM manages the complete SSH chain and keeps control of the keys locally.png)
From what you've written, we understand that it might involve storing the second private key on the jump host. But this way would allow the jump host to connect to the final server independently. It is technically possible, but it is less secure. If the jump host is compromised, it could be used to access the target server directly.
So while RDM might not work exactly like what you had in mind, it provides a similar flow and better security since the keys do not leave the client machine. Please let us know if you need further clarification or have other questions.
Best regards,
Maxim Robert
image (71).png