Credential Management - "LAPS" entry
Hello,
I just discovered that you have a LAPS entry that would allow us to grab the current LAPS password from Active Directory! :)
Is this for "Legacy LAPS", or "Windows LAPS"? I hope the later...
But the more important thing - why do you only have a static username and password field here? We manage the users that are allowed to read LAPS in our Delinea Secret Server which means I would need to select "Linked (user vault)" here and select the needed account from my Secret Server. I hope you can add this functionality to that entry type!
Thanks a lot for your help!
Brgds Andreas
All Comments (4)
Hi,
Yes, the current version of RDM (2024.3) supports both legacy and Windows LAPS.
In Windows LAPS case, for password decryption, the user account running RDM must have the rights to view the LAPS password for the decryption to work.
As for the static username/password, I assumed, looks like wrongly, that a single account would be needed to access LDAP.
In your use case, you store account creds capable of accessing LDAP in Secret Server for each user?
Jonathan Lafontaine
Hello,
Sure - LAPS in RDM works as LAPS normally works. Only the - in our case - group members that have the permission to read the LAPS passwords can read them.
We don´t have a single account that has this permission because we only use personalized accounts. A shared account has some extra risk as it is known by many people and changing the password regularly is also hard. That´s why we avoid to use such accounts.
So yes, every admin with the permission to read LAPS passwords has his own personalized account stored in Secret Server.
Brgds Andreas
I'll open a ticket to investigate potential improvements we can do to our LAPS entry to help your case.
Such improvements could include using the Windows account to access LDAP, which would remove the need for credentials in the LAPS entry.
Also, RDM as a notion of "My Account Settings" that we could be implement for LAPS entry. "My Account Settings", allows each RDM user to provide custom credential for entrys that uses it.
However, RDM currently doesn't have a concept of credential chaining so linking a Secret Server credential stored in the user vault is not possible.
Jonathan Lafontaine
Yes - adding this would be the best solution I think: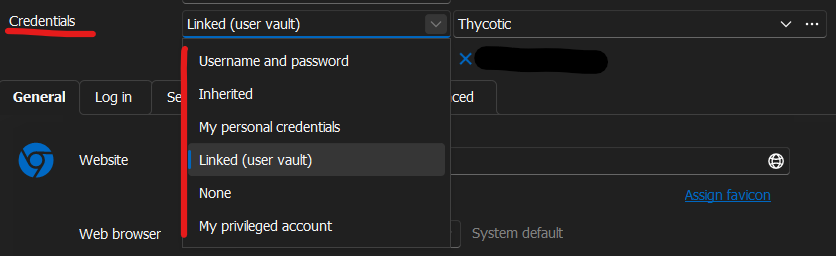
Maybe it would be a good idea to add this to all entries where possible. In our case we try to minimize the passwords needed/known for our users and admins. We use smart card authentication on our clients and everything else must support SSO via kerberos or SAML...
Brgds Andreas
8239d37f-fa43-46ef-b08f-79334854e85e.png