If only one elevation group make it selected
1 vote
Hi,
It would be nice, if there's only one elevation group configured, to make it selected per default on the checkout request (or at least make it configureable if it should be already selected or not ;-).
Users could save two clicks and make the checkout process more efficient.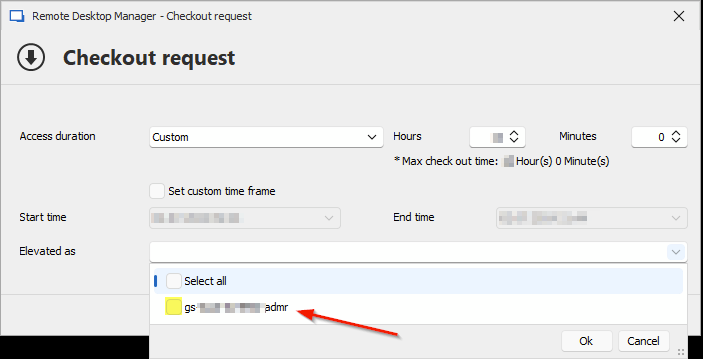
Best regards,
Phil
90866bb6-8ece-477b-947e-ccb02ef50e2c.png
All Comments (9)
Hello Phil,
Thank you for your request. I understand that it could help your users to save 2 clicks, but my fear is that people request privileged that they don't need in other cases and it is something that we would like to avoid. We think that an elevation should always be requested by the user. Adding a configuration could be a solution though, but I would be curious to know a bit more on your use case. If you have only one group, why don't you add the account in that group in the provider ? Your users could only checkout the account without requesting the elevated group and the result would be the same if I understand correctly, am I right ? If you always want to be added to the group, why should we request to be added to the group ? Don't hesitate to let us know more on your use case, we will see how we could help you to avoid annoying clics when you checkout an account.
Best regards,
François Dubois
Hello François,
thanks a lot for your answer.
Maybe I'm also missing something, but let me explain our use case:
We have a tiered Active Directory; the whole domain is separated into 3 tiers (yellow, organge, red) by group policies. Critical assets like domain controllers, backup or CA belong to the red tier. Member servers belong to the orange tier. Client computers belong to the yellow tier. An administrator needs to have a dedicated account per tier, because we want to prevent passing password hashes from one tier to another. He's not allowed to manage a "red server" with his "orange account", etc. This means the administrator might have 3 admin-accounts which he needs to checkout in order to be able to connect/manage the servers or clients.
So I configured 3 JIT Privilege Sets on the provider (one set per tier -> yellow, orange, red) and assigned the corresponding privileged accounts. This leads to the situation when a user requests a checkout for a privileged account, there's always only one elevation group to pick on the checkout request dialog.
I did not see another way to configure this, if we'd like to leverage the JIT feature.
User Accounts Privileged AD Groups ------------------------------------------------------------------------ YellowAdmBob -> Member of Yellow-Admin-Group / Privileged User "Bob" - OrangeAdmBob -> Member of Orange-Admin-Group \ RedAdmBob -> Member of Red-Admin-Group
I hope I could clarify our use case.
Best regards,
Philipp
Hello Philipp,
Thank you for your answer, it helps to understand. But I have one more question. If YellowAdmBob account is always used in the group Yellow-Admin-Group, why don't you add 'YellowAdmBob' in the group ? So you will not have to do an elevation at the checkout. I don't see that as less secure since the password is rotated when you check in the account and nobody will know the password. So is there a reason why you don't want to add the YellowAdmBob account in the group permenently ?
Best regards,
François Dubois
Hello François,
thanks for your answer.
Well, in my opinion password rotation is good, but combined with temporary elevation on a by-request, timed basis is even better. That's the idea of Just-In-Time access, isn't it? It reduces the risk of privileged access abuse and lateral movement when a privileged account not permanently has the elevated rights.
It's also an recurring argument in the discussions with our customers. We ofter hear complaints that for example there are too many permanent members of the Domain Admins group, etc. So we try to follow the principle of least privilege.
Best regards,
Philipp
Hello Philipp,
Thank you for your response. I understand your perspective. I recently discussed similar arguments with our security team, and here is my understanding.
Just-In-Time elevation can be useful if you want to add specific permissions in particular cases. For example, if Bob doesn't need to be part of the Yellow-Admin-Group every time you use it, you could use JIT to add it only when needed. This way, if it's not necessary, you can check out the account and avoid granting unnecessary permissions for your tasks.
If the account always has to be part of the group when you use it, the risk reduction benefit you get with JIT is pretty low. If the account is not checked out and remains "idle" in Devolutions Server, it is safe to assume it just can't be used (assuming the password is changed after check-in, of course). We don't really see scenarios where an attacker would be able to access that account without first compromising something much more privileged (like the server itself or the identity provider). Since the password is randomly generated and strong it will withstand brute force attacks. With that in mind, we consider that having the account, Bob, always in the Yellow-Admin-Group to be as secure as always checking it out with the default group.
Please let me know if this explanation makes sense to you or if you have any questions.
Best regards,
François Dubois
Hi François,
thanks for your explanation.
I understand the argument of your security team, but I don't particularly agree. Even if the benefit of JIT in our scenario is low, it's still a benefit.
As stated above, we have customers which are interessted to keep the amount of members of privileged groups as low as possible. Those customers often go through security audits year by year and it's a common audit control to verify the members of privileged groups (such as domain admins). If we, as a service provider, can offer the JIT functionality towards our customers, we are very welcome.
But thanks for your statements, I think we can close this thread :-)
Best regards,
Philipp
Hi Philipp,
I just read my answer again and noticed that one paragraph was missing. It was a paragraph to specify that there are scenarios where it could be useful to have the requested feature. So, I was not trying to tell you that it doesn't make sense to do it, but I wanted to let you know why it will not be a priority for us in the short term. However, it would make sense to have that feature in cases where you have to go through security audits and the entire business is using JIT. It will be easier to follow that way of working instead of documenting that specific group and explaining why you always let the user remain in the group.
In conclusion, when we will implement it, it will probably be a user setting to always select the group so the user can do it by himself and understand why he wants it that way. It will be more of a productivity improvement feature than a security feature, if you understand what I mean. I'll keep that in mind and will see how it could be integrated later with our other developments.
Don't hesitate if you have questions.
Best regards,
François Dubois
Hi, i also think this feature could be beneficial and provide a much better experience for users, when only one possible elevation is available.
I also work in a tiered environment and having the option to set a default elevation would make for a far more seamless experience.