v2023.3.39.0 64-bit - Cylance blocking/flagging SSH.exe
FYI for version 2023.3.39.0 64-bit
the AV: Cylance is blocking/flagging
"C:\Program Files\Devolutions\Remote Desktop Manager\runtimes\win-x64\native\ssh.exe"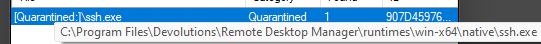
Knowing Cylance, it's a Cylance problem, but thought you might want to know in case it persists/there are other cases.
7bf86306-e7c7-4753-b1a1-94256b968ba3.png
All Comments (4)
Hello,
Thank you for reaching out to us regarding this,
Our security team has performed a scan on SSH.exe on their end and it returned without any issues, could you provide us with the Hash value of your file so that we can validate it?
Microsoft has the following article explaining how to retrieve this:
Get-FileHash (Microsoft.PowerShell.Utility) - PowerShell | Microsoft Learn
Let me know,
Best regards,
Samuel Dery
At this time I do not have access to it because of Cylance.
It was whatever SSH.exe resource came through on the last automatic update for version 2023.3.39.0 ~ 2/21/2024.
I'll work with the Cylance operate to get it released and get the hash.
Any preferred hash standard? MD5/SHA256?
SHA256: 907d459762e17889ab48a6193d13fb3bca99e40df9d0c14ee0cc4986db800e39
MD5: E05635AAC02F13D59D2FC71D7E9D4C8A
Hi,
SHA256 would be obviously preferred, but is there a way to allow the ssh.exe executable by signer certificate instead? This is our own Win32-OpenSSH distribution, code signed by Devolutions. However, with the current release process we sign ssh.exe with RDM, rather than import the same ssh.exe signed once, so the hash will keeping changing. I take note that we should improve the build process to sign our Win32-OpenSSH distribution in the original nuget package to reduce the amount of times the hash would change, but it is still a possibility given that we could update it at any time.
Best regards,
Marc-André Moreau
