ERRCONNECT_SECURITY_NEGO_CONNECT_FAILED
Hi,
Since the start of this year (possibly since the January RDM release), I've been unable to connect to the majority of my Windows Servers through RDP.
I'm seeing the following in the session logs:
[17:13:20:917] [36096:6f69f000] [INFO][Devolutions.Rdp.Credentials] - [Parse]: parsing "j******", "A*****" (Mstsc) => "Username: "j******" Domain: "A*****"" [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.core] - [freerdp_connect_begin]: resetting error state [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpdr [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpsnd [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMJump [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMCmd [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMLog [17:13:20:920] [36096:6f69f000] [DEBUG][com.freerdp.channels.channels.cliprdr.client] - [cliprdr_VirtualChannelEntryEx]: VirtualChannelEntryEx [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx cliprdr [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.channels.drdynvc.client] - [drdynvc_VirtualChannelEntryEx]: VirtualChannelEntryEx [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx drdynvc [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpdr [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpsnd [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMJump [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMCmd [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMLog [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx cliprdr [17:13:20:921] [36096:6f69f000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:20:921] [36096:6f69f000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx drdynvc [17:13:20:921] [36096:6f69f000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:20:921] [36096:6f69f000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:20:921] [36096:6f69f000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:20:123] [36096:6f69f000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: primitives benchmark result: [17:13:20:274] [36096:6f69f000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: * generic= 96 [17:13:20:425] [36096:6f69f000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: * optimized= 490 [17:13:20:425] [36096:6f69f000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: primitives autodetect, using optimized [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_set_negotiation_enabled]: Enabling security layer negotiation: TRUE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_set_restricted_admin_mode_required]: Enabling restricted admin mode: FALSE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_enable_rdp]: Enabling RDP security: TRUE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_enable_tls]: Enabling TLS security: TRUE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_enable_nla]: Enabling NLA security: TRUE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_enable_ext]: Enabling NLA extended security: FALSE [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_enable_rdstls]: Enabling RDSTLS security: FALSE [17:13:20:426] [36096:6f69f000] [WARN][com.freerdp.core.nego] - [nego_enable_aad]: This build does not support AAD security, disabling. [17:13:20:426] [36096:6f69f000] [DEBUG][com.freerdp.core.rdp] - [rdp_client_transition_to_state][0x14e8d4200]: CONNECTION_STATE_INITIAL --> CONNECTION_STATE_NEGO [17:13:20:427] [36096:6f69f000] [DEBUG][com.freerdp.core] - [freerdp_tcp_is_hostname_resolvable]: resetting error state [17:13:20:428] [36096:6f69f000] [DEBUG][com.freerdp.core] - [freerdp_tcp_default_connect]: resetting error state [17:13:20:428] [36096:6f69f000] [DEBUG][com.freerdp.core] - [freerdp_tcp_default_connect]: connecting to peer 127.0.0.1 [17:13:20:443] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_connect]: state: NEGO_STATE_NLA [17:13:20:443] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_attempt_nla]: Attempting NLA security [17:13:20:443] [36096:6f69f000] [DEBUG][com.freerdp.core.nego] - [nego_send_negotiation_request]: RequestedProtocols: 3 [17:13:20:481] [36096:6f69f000] [ERROR][com.freerdp.core.transport] - [parse_default_mode_pdu]: fast path - invalid pduLength: 0 [17:13:20:481] [36096:6f69f000] [ERROR][com.freerdp.core.nego] - [nego_connect]: Protocol Security Negotiation Failure [17:13:20:481] [36096:6f69f000] [ERROR][com.freerdp.core] - [rdp_client_connect]: ERRCONNECT_SECURITY_NEGO_CONNECT_FAILED [0x0002000C] [17:13:20:481] [36096:6f69f000] [ERROR][com.freerdp.core.connection] - [rdp_client_connect]: Error: protocol security negotiation or connection failure [17:13:20:483] [36096:6f69f000] [DEBUG][com.freerdp.core.rdp] - [rdp_finalize_reset_flags][0x14e8d4200]: [CONNECTION_STATE_NEGO] reset finalize_sc_pdus [17:13:20:483] [36096:6f69f000] [DEBUG][com.freerdp.core.rdp] - [rdp_client_transition_to_state][0x14e8d4200]: CONNECTION_STATE_NEGO --> CONNECTION_STATE_INITIAL [17:13:21:701] [36098:6e1d3000] [INFO][Devolutions.Rdp.Credentials] - [Parse]: parsing "j******", "A*****" (Mstsc) => "Username: "j******" Domain: "A*****"" [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.core] - [freerdp_connect_begin]: resetting error state [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpdr [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpsnd [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMJump [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMCmd [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMLog [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.channels.channels.cliprdr.client] - [cliprdr_VirtualChannelEntryEx]: VirtualChannelEntryEx [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx cliprdr [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.channels.drdynvc.client] - [drdynvc_VirtualChannelEntryEx]: VirtualChannelEntryEx [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx drdynvc [17:13:21:703] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:703] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpdr [17:13:21:703] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx rdpsnd [17:13:21:704] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMJump [17:13:21:704] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMCmd [17:13:21:704] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx RDMLog [17:13:21:704] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx cliprdr [17:13:21:704] [36098:6e1d3000] [WARN][com.freerdp.core.client] - [freerdp_channels_client_load_ex]: Skipping, channel already loaded [17:13:21:704] [36098:6e1d3000] [DEBUG][com.freerdp.client.common.cmdline] - [freerdp_client_load_static_channel_addin]: loading channelEx drdynvc [17:13:21:704] [36098:6e1d3000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:21:704] [36098:6e1d3000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:21:704] [36098:6e1d3000] [ERROR][com.freerdp.channels.virtual.channel] - [virtchan_virtual_channel_init_event_ex]: Unhandled event type 0 [17:13:21:905] [36098:6e1d3000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: primitives benchmark result: [17:13:21:57] [36098:6e1d3000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: * generic= 96 [17:13:21:207] [36098:6e1d3000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: * optimized= 487 [17:13:21:207] [36098:6e1d3000] [DEBUG][com.freerdp.primitives] - [primitives_autodetect_best]: primitives autodetect, using optimized [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_set_negotiation_enabled]: Enabling security layer negotiation: TRUE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_set_restricted_admin_mode_required]: Enabling restricted admin mode: FALSE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_enable_rdp]: Enabling RDP security: TRUE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_enable_tls]: Enabling TLS security: TRUE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_enable_nla]: Enabling NLA security: FALSE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_enable_ext]: Enabling NLA extended security: FALSE [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_enable_rdstls]: Enabling RDSTLS security: FALSE [17:13:21:209] [36098:6e1d3000] [WARN][com.freerdp.core.nego] - [nego_enable_aad]: This build does not support AAD security, disabling. [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core.rdp] - [rdp_client_transition_to_state][0x134835600]: CONNECTION_STATE_INITIAL --> CONNECTION_STATE_NEGO [17:13:21:209] [36098:6e1d3000] [DEBUG][com.freerdp.core] - [freerdp_tcp_is_hostname_resolvable]: resetting error state [17:13:21:210] [36098:6e1d3000] [DEBUG][com.freerdp.core] - [freerdp_tcp_default_connect]: resetting error state [17:13:21:210] [36098:6e1d3000] [DEBUG][com.freerdp.core] - [freerdp_tcp_default_connect]: connecting to peer 127.0.0.1 [17:13:21:224] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_connect]: state: NEGO_STATE_TLS [17:13:21:224] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_attempt_tls]: Attempting TLS security [17:13:21:224] [36098:6e1d3000] [DEBUG][com.freerdp.core.nego] - [nego_send_negotiation_request]: RequestedProtocols: 1 [17:13:21:269] [36098:6e1d3000] [ERROR][com.freerdp.core.transport] - [parse_default_mode_pdu]: fast path - invalid pduLength: 0 [17:13:21:269] [36098:6e1d3000] [ERROR][com.freerdp.core.nego] - [nego_connect]: Protocol Security Negotiation Failure [17:13:21:269] [36098:6e1d3000] [ERROR][com.freerdp.core] - [rdp_client_connect]: ERRCONNECT_SECURITY_NEGO_CONNECT_FAILED [0x0002000C] [17:13:21:269] [36098:6e1d3000] [ERROR][com.freerdp.core.connection] - [rdp_client_connect]: Error: protocol security negotiation or connection failure [17:13:21:270] [36098:6e1d3000] [DEBUG][com.freerdp.core.rdp] - [rdp_finalize_reset_flags][0x134835600]: [CONNECTION_STATE_NEGO] reset finalize_sc_pdus [17:13:21:270] [36098:6e1d3000] [DEBUG][com.freerdp.core.rdp] - [rdp_client_transition_to_state][0x134835600]: CONNECTION_STATE_NEGO --> CONNECTION_STATE_INITIAL
All Comments (16)
Hello
Thanks for the issue report. One thing that stands out is:
connecting to peer 127.0.0.1
You're connecting to the localhost address, so I have to assume some kind of tunnel is being used? Can you provide any details?
Or maybe you're connecting to a hostname that is for some reason resolving to localhost?
The error is a bad (actually missing / 0 length) response from the server, so this does appear to be going wrong somewhere at the network level rather than in the RDP protocol itself.
Please let me know if you have any questions or something isn't clear!
Thanks and kind regards,
Richard Markievicz
Hi Richard,
Correct, I'm doing a SSH tunnel to a jumpbox and then RDP through that.
[1/30/2024 5:13:20 PM] Sending forward channel open request: 0/- XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:20 PM] Received channel open confirmation: 0/3 WS 200000/262144 MPS 32000/65536 [1/30/2024 5:13:20 PM] Successfully established connection 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:20 PM] Local read error, ending connection 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [(54) Connection reset by peer] [1/30/2024 5:13:20 PM] Sending channel close request: 0/3 [1/30/2024 5:13:20 PM] Received channel close request: 0/3 [1/30/2024 5:13:20 PM] Channel is closed: 0/3 [1/30/2024 5:13:20 PM] Closed tunnel: 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:20 PM] Sending forward channel open request: 0/- XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:20 PM] Received channel open confirmation: 0/4 WS 200000/262144 MPS 32000/65536 [1/30/2024 5:13:20 PM] Successfully established connection 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:20 PM] Sending channel EOF: 0/4 [1/30/2024 5:13:21 PM] Received channel EOF: 0/4 [1/30/2024 5:13:21 PM] Sending channel close request: 0/4 [1/30/2024 5:13:21 PM] Received channel close request: 0/4 [1/30/2024 5:13:21 PM] Channel is closed: 0/4 [1/30/2024 5:13:21 PM] Closed tunnel: 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:21 PM] Sending forward channel open request: 0/- XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:21 PM] Received channel open confirmation: 0/5 WS 200000/262144 MPS 32000/65536 [1/30/2024 5:13:21 PM] Successfully established connection 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389 [1/30/2024 5:13:21 PM] Sending channel EOF: 0/5 [1/30/2024 5:13:21 PM] Received channel EOF: 0/5 [1/30/2024 5:13:21 PM] Sending channel close request: 0/5 [1/30/2024 5:13:21 PM] Received channel close request: 0/5 [1/30/2024 5:13:21 PM] Channel is closed: 0/5 [1/30/2024 5:13:21 PM] Closed tunnel: 127.0.0.1:12006 -> XXX.XXX.XXX.XXX:3389
Hi jimmilarsen,
Do you launch your tunnel in RDM? Could you try by launching the tunnel in an instance of the Terminal app? Like so:
ssh -L <localport>:<remotehost>:<remoteport> <user>@<sshhost> -p <sshport>
Does the RDP entry still fails to connect?
I want to identify if the issue is with the RDP entry, or with the SSH Tunnel entry.
Best regards,
Xavier Fortin
Hi Xavier,
I'm launching the tunnel through RDM. It's actually a double hop, so the connection would be like this:
Macbook -> Local Jumpbox -> Remote Jumpbox -> Remote RDP
I'm not sure how I would replicate this through the SSH terminal :)
I can email you screenshots of the config for the Tunnel and the RDP connections if that helps.
Hi,
I think you could possibly make this work like so:
ssh -L <localport>:<sessionhost>:<sessionport> -J <sshuser1>@<sshhost1>:<sshport1> <sshuser2>@<sshhost2> -p <sshport2>
Best regards,
Xavier Fortin
Hi Xavier,
Is this not the same as connecting to the tunnel directly in RDM like so:
[1/31/2024 3:34:34 PM] Devolutions Protocols version: 2024.1.9.1 macOS [1/31/2024 3:34:34 PM] Terminal font: Menlo [Menlo, fixed=True] [1/31/2024 3:34:34 PM] Starting SSH, verbose level: 2 [1/31/2024 3:34:34 PM] Setting up connection [1/31/2024 3:34:34 PM] Using jump host: XXX.XXX.XXX.XXX:22, 0 [1/31/2024 3:34:34 PM] Connecting to port: 22 (IP any) [1/31/2024 3:34:34 PM] Connected to SSH proxy host [1/31/2024 3:34:34 PM] SSH banner: SSH-2.0-OpenSSH_7.6p1 Ubuntu-4ubuntu0.7 [1/31/2024 3:34:34 PM] Sending kex init [1/31/2024 3:34:34 PM] Received kex init [1/31/2024 3:34:34 PM] Selected algorithms: curve25519-sha256, ssh-ed25519, chacha20-poly1305@openssh.com, chacha20-poly1305@openssh.com, implicit by cipher, implicit by cipher, none, none [1/31/2024 3:34:34 PM] Sending Ed25519 kex init [1/31/2024 3:34:34 PM] Received Ed25519 kex reply [1/31/2024 3:34:34 PM] Successfully authentified server [1/31/2024 3:34:34 PM] Sending new keys message [1/31/2024 3:34:34 PM] Received new keys message [1/31/2024 3:34:34 PM] Sending userauth service request [1/31/2024 3:34:34 PM] Received extension info message [1/31/2024 3:34:34 PM] Server accepts public key types: ssh-ed25519,ssh-rsa,rsa-sha2-256,rsa-sha2-512,ssh-dss,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521 [1/31/2024 3:34:34 PM] Received service accepted message [1/31/2024 3:34:34 PM] Sending userauth init request [1/31/2024 3:34:34 PM] Received userauth failure: keyboard-interactive [1/31/2024 3:34:34 PM] Starting interactive authentication [1/31/2024 3:34:34 PM] Sending userauth interactive request [1/31/2024 3:34:34 PM] Received userauth info request: [Prompt->Password: ] [1/31/2024 3:34:34 PM] Sending userauth interactive response: 1 [1/31/2024 3:34:42 PM] Received userauth info request: [1/31/2024 3:34:42 PM] Sending userauth interactive response: 0 [1/31/2024 3:34:42 PM] Received userauth success [1/31/2024 3:34:42 PM] User authenticated successfuly by password interactive [1/31/2024 3:34:42 PM] Sending forward channel open request: 0/- YYY.YYY.YYY.YYY:22 [1/31/2024 3:34:43 PM] Received global request: hostkeys-00@openssh.com , no need to reply [1/31/2024 3:34:43 PM] Received channel open confirmation: 0/0 WS 200000/2097152 MPS 32000/32768 [1/31/2024 3:34:44 PM] SSH banner: SSH-2.0-8.48 FlowSsh: Bitvise SSH Server (WinSSHD) 8.48: free only for personal non-commercial use [1/31/2024 3:34:44 PM] Sending kex init [1/31/2024 3:34:44 PM] Received kex init [1/31/2024 3:34:44 PM] Selected algorithms: curve25519-sha256, rsa-sha2-256, aes256-ctr, aes256-ctr, hmac-sha2-256, hmac-sha2-256, none, none [1/31/2024 3:34:44 PM] Sending Ed25519 kex init [1/31/2024 3:34:44 PM] Received Ed25519 kex reply [1/31/2024 3:34:44 PM] Successfully authentified server [1/31/2024 3:34:44 PM] Sending new keys message [1/31/2024 3:34:44 PM] Received new keys message [1/31/2024 3:34:44 PM] Sending userauth service request [1/31/2024 3:34:44 PM] Received extension info message [1/31/2024 3:34:44 PM] Server accepts public key types: ssh-ed25519,ecdsa-sha2-1.3.132.0.10,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,rsa-sha2-512,rsa-sha2-256,ssh-rsa [1/31/2024 3:34:44 PM] Received service accepted message [1/31/2024 3:34:44 PM] Sending userauth init request [1/31/2024 3:34:44 PM] Received userauth failure: publickey,keyboard-interactive,password [1/31/2024 3:34:44 PM] Starting interactive authentication [1/31/2024 3:34:44 PM] Sending userauth interactive request [1/31/2024 3:34:44 PM] Received userauth info request: [Name->Password authentication] [Prompt->Password: ] [1/31/2024 3:34:44 PM] Sending userauth interactive response: 1 [1/31/2024 3:34:51 PM] Received userauth success [1/31/2024 3:34:51 PM] User authenticated successfuly by password interactive [1/31/2024 3:34:51 PM] Listening on 127.0.0.1:12006 D
From what I can see, the SSH Tunnels are working as expected, it's the final RDP hop that's causing issues.
Hi Xavier,
Just to add, there has been no changes to the data sources in RDM nor any changes to the servers themselves.
This was working for me in RDM 2023.3.10.2, but since upgrading to 2023.3.11.4 and 2023.3.12.2 it's no longer working for me.
EDIT: Just tried rolling back to 2023.3.10.2 and it's working again, so something must've changed in the versions after.
Is this not the same as connecting to the tunnel directly in RDM like so:
Yes, this is the point. I'm trying to confirm if there is an issue specifically with the Tunnel entry (our tunnel entry). Richard, earlier, seems to believe that the error occurs outside of the RDP protocol, i.e. in the communication in between, so in the tunnel forwarding. Hence why I'm making you do this test. I need to know where we should concentrate our investigation since it concerns two different teams.
And I need you to test this, because I have no issue on my side, so I cannot reproduce the issue myself.
Best regards,
Xavier Fortin
Hi Xavier,
I ran the ssh command you asked, like so:
ssh -L 12006:ZZZ.ZZZ.ZZZ.ZZZ:3389 -J jimmilarsen@YYY.YYY.YYY.YYY:22 jimmilarsen@XXX.XXX.XXX.XXX -p 22
XXX.XXX.XXX.XXX : local jumpbox server IP
YYY.YYY.YYY.YYY : remote jumpbox server IP
ZZZ.ZZZ.ZZZ.ZZZ : remote RDP server IP
I then created a new RDP session to 127.0.0.1:12006 and I was able to RDP to the remote RDP server.
Alright, so it should confirm that the issue is on our SSH Tunnel.
I'll keep in touch with the proper team.
We'll post back when we have more info.
Best regards,
Xavier Fortin
Thanks Xavier :)
Hi Jimmilarsen,
Do you remember when this stopped working exactly? And did it coincide with an update of RDM?
Do you use the "Use over secure gateway" feature? Here is a screenshot: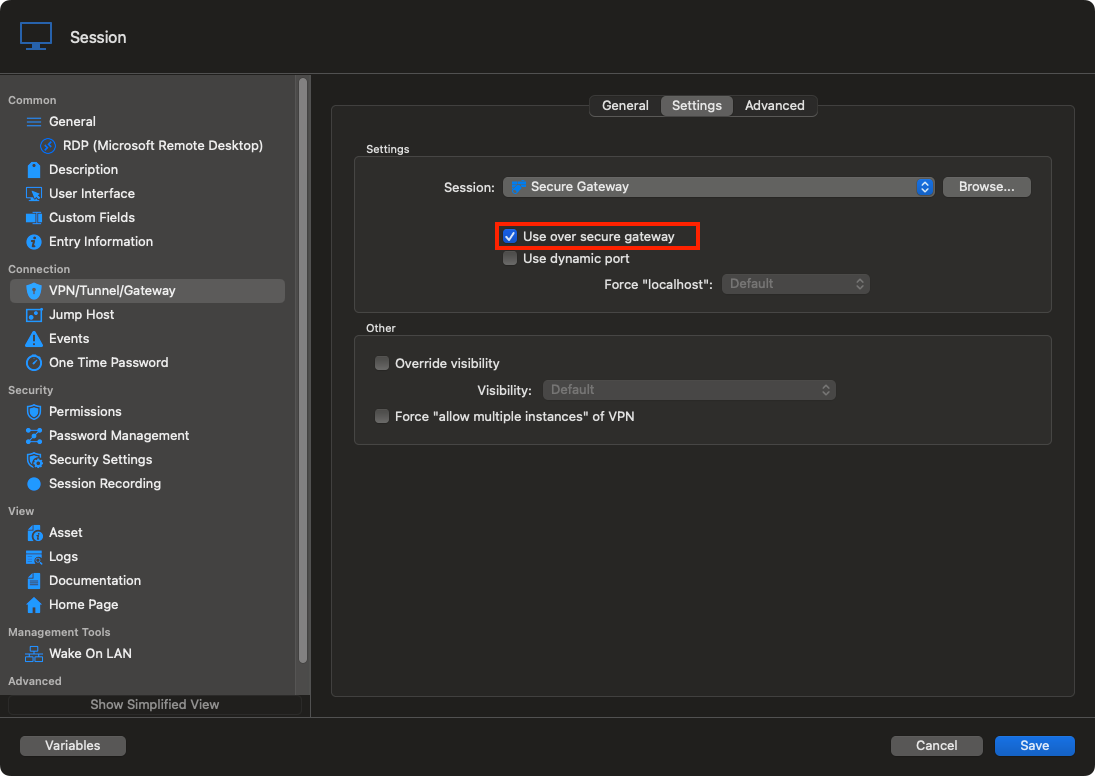
Best regards,
Xavier Fortin
UseOverSecureGateway.png
Hi Xavier,
It was working for me in RDM 2023.3.10.2, but it stopped working after upgrading to 2023.3.11.4 and it is the same in 2023.3.12.2.
Rolling back to 2023.3.10.2 and it's working again.
I do have 'Use over secure gateway' ticked, as far as I recall, it was never working without.
Kind Regards
Jimmi Larsen
Alright, I did not realize this at first. It's already a known issue then. And this one we can reproduce. We'll keep you posted on our progress.
Best regards,
Xavier Fortin
Hello,
Your issue should be solved in our latest version of RDM Mac (2023.3.13.4)
If there's anything, don't hesitate to communicate with us.
Best regards,
Michel Lambert
Hi Michel,
I just upgraded to RDM version 2023.3.13.4 and looks like we're back in business.
Thank you all very much for support on this issue.
Kind Regards
Jimmi Larsen