RDM Update server blocked by Synology Safe Access?
Hi all - I'm using RDM behind a Synology RT6600ax router with a "Safe Access" package that blocks outgoing access to a list of servers identified by Synology's "Threat Intelligence" database and Google Safe Browsing as malicious. I've looked for sourcing on the Threat Intelligence database, but haven't come up with much I would call definitive.
I recently tried to update RDM on a couple of machines, and the RDM Updater app is triggering a Safe Access alert when communicating with a server at 152.195.19.97. This is the IP for cdn.devolutions.net, and this IP is listed in AbuseIPDB as recently hosting malicious activity - see: https://www.abuseipdb.com/check/152.195.19.97. Downloading the update directly or using the "download update using your default browser" option go to the same IP.
This is concerning. I realize IPs get reused, etc, but as the old saying goes, Caesar's wife must be above reproach, and I'd like to get some kind of reassurance that we are not seeing some kind of supply-chain attack here. RDM must be by its nature an attractive target for things like this. I'm sure I'm just being a little paranoid, but as another old saying goes, just because you're paranoid doesn't mean they aren't out to get you.
Any comments here from others seeing anything similar?
All Comments (5)
Hello,
I have forwarded your post to our internal security team. We will investigate why the CDN IP is flagged. You can verify the hash on our website. We also take supply chain attack seriously. Thank you for letting us know.
Regards
David Hervieux
cdn.devolutions.net is pointing to Azure CDN, it is an alias for cdndevolutions.azureedge.net My guess would be that this IP is used to host multiple domains or was previously used for nefarious purposes.
As an additional security measure, the Devolutions Updater is verifying that updates are signed with our code signing certificate before installing. When downloading manually, we provide the SHA-256 hashes of the files if you want to double check them before installation.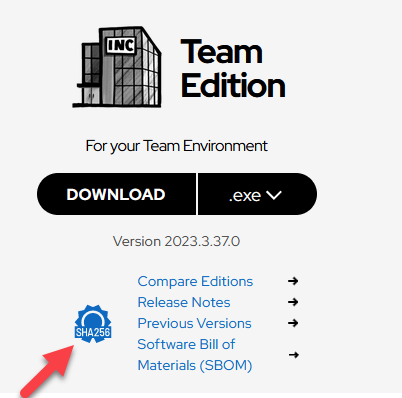
Sébastien Duquette
b58de7a0-a945-47f4-beb5-298cf6167f06.png
I understand and appreciate the seriousness with which you take the security of the product and your users. I have used the SHA256 values and compared to the downloaded MSI and ZIP files and found no issues, and I am happily running 2023.3.37.0 as we speak.
I have no doubt that the IP is flagged for reasons having nothing to do with you, but it is flagged, and not just by Synology. I hope that you as an Azure CDN customer (which I am not) can let Microsoft know this is the case, and I look forward to taking the IP out of my exceptions list when this issue is corrected.
Thanks for your attention to this matter, and best wishes for continued success!
Hi Solmssen,
My name is David from the security department.
Thanks a lot for flagging the issue with the RDM update server and Synology Safe Access.
We appreciate you taking the time to let us know. It's super helpful.
We're planning to get in touch with Microsoft to see how we can sort this out.
If you've got any more insights or questions, feel free to drop us a message.
Regards,
David Grandolfo
Hi David - thanks so much for letting me know this is helpful. Good luck with Microsoft!