Alternate MFA option like RDM (YubiKey, Duo, TOTP) instead of backup codes only
Alternate MFA option like RDM (YubiKey, Duo, TOTP) instead of backup codes only
5 votes
We just migrated from RDM backed by SQL to RDM backed by DVLS for better security of our datasource.
One thing I am confused on is why the only MFA alternate is Backup Codes and Email, we don't want email setup, which leaves us only with Backup Codes.
Currently in RDM we have a mix of MFA options setup, YubiKey Primary, Duo for when YubiKey is not around and TOTP as a last resort if internet is down.
Problem is DVLS will only allow you to pick one MFA option to setup, its would be great if there was a way to allow the user to pick at time of auth on the DVLS page to choose Duo if the user does not have their YubiKey with them instead of needing to rely on Backup codes. (We lock down web portal access so if a user burns through the backup codes we have to re-enable the web login perms. then allow them to generate codes, then we have to remove the web portal access...not ideal and much slower needing to get codes out of our PW Manager app on mobile.
The web portal already has the alternate MFA button and a dropdown for codes or email...so the GUI is already ready for this feature :-) Would be great to see the above as an option for us at some point in the future.
Thank you,
-Derek
All Comments (20)
Hello Derek,
I have created a feature request on our side. We will discuss internaly to see how easy it could be and write back here if we work on a such feature.
Best regards,
François Dubois
Thank you François, appreciate it
Hi
Is there any update on this? It would be great to be able to for example have Duo as primary MFA and TOTP as a backup. As it is now the first one is removed if I add another form of MFA.
Hello,
Thank you for your interest. Unfortunately, we don't have an ETA for that feature. We are planning our next development cycle soon, we will see what could be done with our other priorities.
Best regards,
François Dubois
We're interested in having a backup key either. Here to subscribe and follow.
Hello @kmdkeen,
Devolutions Server already supports Backup codes as alternate 2FA. Is what what you are looking for ?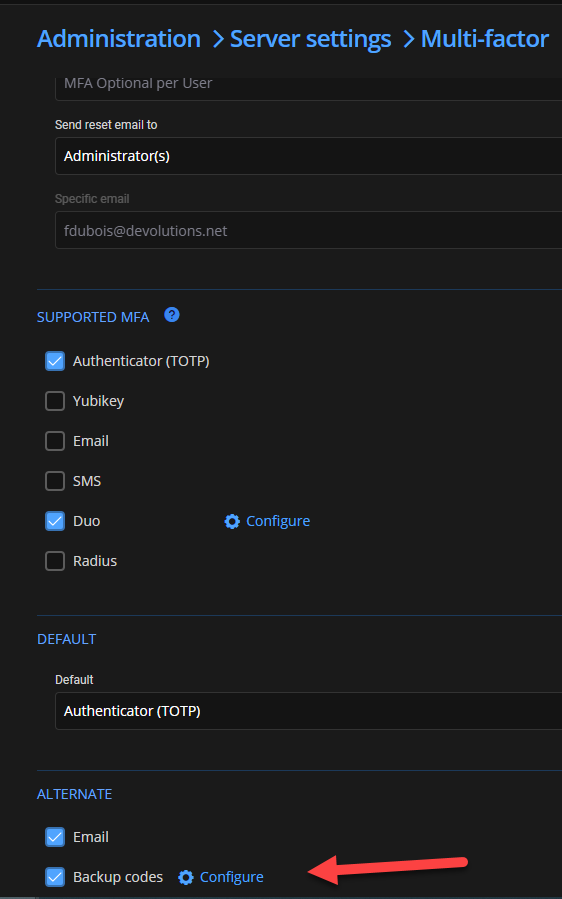
Best regards,
François Dubois
9770331e-815c-4656-ad2f-4318c4c6e4f2.png
Hey François,
no! These are the text-based backup-codes. We're looking for another (spare) yubikey as a backup-key.
Best regards!
Hello,
Oh, sorry, I misunderstood. Thank you for letting us know.
Best regards,
François Dubois
Is there anything new yet? We also need to take care of a 2nd Yubikey.
Best regards!
Hello,
I don't have an official ETA for that, I can't promise, but we will try to squeeze it into the next release 2025.2 planned for June.
Best regards,
François Dubois
We would like this feature as well, Primary Yubikey and Secondary TOTP or SMS
We would also be happy to get this feature. We are using Yubikey OTP as a strong and convenient primary MFA provider, but we need some alternative if someone forgot the Yubikey or can't use it for whatever reason. The current alternatives are either unsecure (E-Mail) or not complicated to handle (Backup codes).
Being able to select one of the MFA providers currently available as primary ones also as an alternate one would be sufficient for us. In that case we could select TOTP as alternate provider, so that users have two different options to sign in with.
François Dubois we hope you can make happy us :)
Hello,
Thank you for your interest. It will probably not be part of 2025.2 planned in June because we have a lot of work ahead of us, but it should be part of our next development cycle. I'm keeping that improvement in mind; we will post back here once we have an update.
Best regards,
François Dubois
Hello,
Thank you for your interest. It will probably not be part of 2025.2 planned in June because we have a lot of work ahead of us, but it should be part of our next development cycle. I'm keeping that improvement in mind; we will post back here once we have an update.
Best regards,
I am glad this is finally getting some traction, we have had this happen quite a few times since I posted and the one-time burnable codes are too cumbersome to deal with vs TOTP.
Much appreciate the working this into release at some point, will be a welcomed change for many, I am sure.
-Derek
+1 for this request.
+1 for this request.
@mad
I do really hope they work this in, it comes up quite a bit for out small team, someone works from home and forgets their yubikey...one of us needs to go in and reset for them to totp as you can't use both and pick between (but can in RDM).
Hi everyone,
We have good news to share on this front, in our next release 2026.1, users will be able to set any combination of MFA factors at once. Allowing you to combine TOTP, Yubikey, SMS and more if you'd like. We're also adding Passkey support to the growing list of factors.
This is only phase 1 of modernizing Devolutions Server's authentication, phase 2 which is TBD, will allow users to set multiple factors of the same type as well. (special shout out to our very patient users dual wielding Yubikeys).
Cheers,
Luc Fauvel
Hi everyone,
We have good news to share on this front, in our next release 2026.1, users will be able to set any combination of MFA factors at once. Allowing you to combine TOTP, Yubikey, SMS and more if you'd like. We're also adding Passkey support to the growing list of factors.
This is only phase 1 of modernizing Devolutions Server's authentication, phase 2 which is TBD, will allow users to set multiple factors of the same type as well. (special shout out to our very patient users dual wielding Yubikeys).
Cheers,
@Luc Fauvel
This great news, appreciate the support and listening to feedback!
Hi everyone,
We have good news to share on this front, in our next release 2026.1, users will be able to set any combination of MFA factors at once. Allowing you to combine TOTP, Yubikey, SMS and more if you'd like. We're also adding Passkey support to the growing list of factors.
This is only phase 1 of modernizing Devolutions Server's authentication, phase 2 which is TBD, will allow users to set multiple factors of the same type as well. (special shout out to our very patient users dual wielding Yubikeys).
Cheers,
@Luc Fauvel
This great news, appreciate the support and listening to feedback!
@dromano
100% Agree. Thank you!