Protected Users Security Group (AD)
Hello,
If the user account is added to the Protected Users group, it is impossible to authenticate using RDM. This problem does not exist on the version for Windows.
Application log:
[24.09.2018 11:39:09 - 5.5.1.0 64-bit]ERROR ERRCONNECT_ACCOUNT_RESTRICTION (0x00000017)
Session Log:
[12:05:25:027] [51640:07b4a000] [DEBUG][com.freerdp.channels.cliprdr.client] - VirtualChannelEntryEx
[12:05:25:027] [51640:07b4a000] [INFO][com.freerdp.client.common.cmdline] - loading channelEx cliprdr
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling security layer negotiation: TRUE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling restricted admin mode: FALSE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling RDP security: TRUE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling TLS security: TRUE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling NLA security: TRUE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Enabling NLA extended security: FALSE
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - state: NEGO_STATE_NLA
[12:05:25:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Attempting NLA security
[12:05:26:034] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - RequestedProtocols: 3
[12:05:26:038] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - RDP_NEG_RSP
[12:05:26:038] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - selected_protocol: 2
[12:05:26:038] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - state: NEGO_STATE_FINAL
[12:05:26:039] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - Negotiated NLA security
[12:05:26:039] [51640:07b4a000] [DEBUG][com.freerdp.core.nego] - nego_security_connect with PROTOCOL_NLA
[12:05:35:026] [51640:07b4a000] [DEBUG][com.winpr.sspi] - InitSecurityInterfaceExA
[12:05:35:027] [51640:07b4a000] [DEBUG][com.freerdp.core.nla] - nla_client_init 348 : packageName=Negotiate ; cbMaxToken=12256
[12:05:35:027] [51640:07b4a000] [DEBUG][com.freerdp.core.nla] - Sending Authentication Token
...
...
[12:05:35:028] [51640:07b4a000] [DEBUG][com.freerdp.core.nla] - CredSSP protocol support 6, peer supports 6
[12:05:35:029] [51640:07b4a000] [DEBUG][com.freerdp.core.nla] - Sending Authentication Token
...
...
[12:05:36:035] [51640:07b4a000] [ERROR][com.freerdp.core] - freerdp_set_last_error ERRCONNECT_ACCOUNT_RESTRICTION [0x00020017]
[12:05:36:035] [51640:07b4a000] [ERROR][com.freerdp.core.rdp] - rdp_recv_callback: CONNECTION_STATE_NLA - nla_recv_pdu() fail
[12:05:36:035] [51640:07b4a000] [ERROR][com.freerdp.core.transport] - transport_check_fds: transport->ReceiveCallback() - -1
[12:05:36:035] [51640:07b4a000] [DEBUG][com.freerdp.core.rdp] - transport_check_fds() - -1
For some reason, the debug in the profiler does not show anything:
Connection States: Refresh...
CreateConnectionStateDictionary : 0 ms
Connection States: Refresh : 5 ms
The problem disappears if you delete a user of their group.
App: Remote Desktop Manager Free (5.5.1.0)
RDP engine = Legacy
Activate sandboxing = True
All Comments (10)
Hi,
We'll look into configuring a server on our side and I'll get back with you when I get more news.
Best regards,
Xavier Fortin
Hi,
After further investigation, at this moment, this seems to be a limitation with FreeRDP. We'll keep the issue opened, but this is unlikely to be fixed until further progress on the FreeRDP side.
Best regards,
Xavier Fortin
Hey Xavier,
Just for reference, I entered an upstream feature request with FreeRDP.
Thanks for pointing me in the right direction!
Hi,
Subscribed to it this instant.
Best regards,
Xavier Fortin
HI Xavier, I am having the same exact issue. I do use the free program and just downloaded the enterprise 30 day trial. what settings do we need to change to make this work?
Hi,
Is your user part of the Protected Users security group? If so, this is not supported by FreeRDP (the component used by RDM to launch RDP sessions in embedded mode). I can only suggest launching those sessions externally with Microsoft Remote Desktop.
altrhombus opened a ticket on the FreeRDP page.
Also, is this the same issue as the one you reported here?
Best regards,
Xavier Fortin
Hi,
For anyone still wondering about this, this should now be possible by setting the SSPI Module setting to Portable and the Authentication Package to Kerberos in an RDP entry: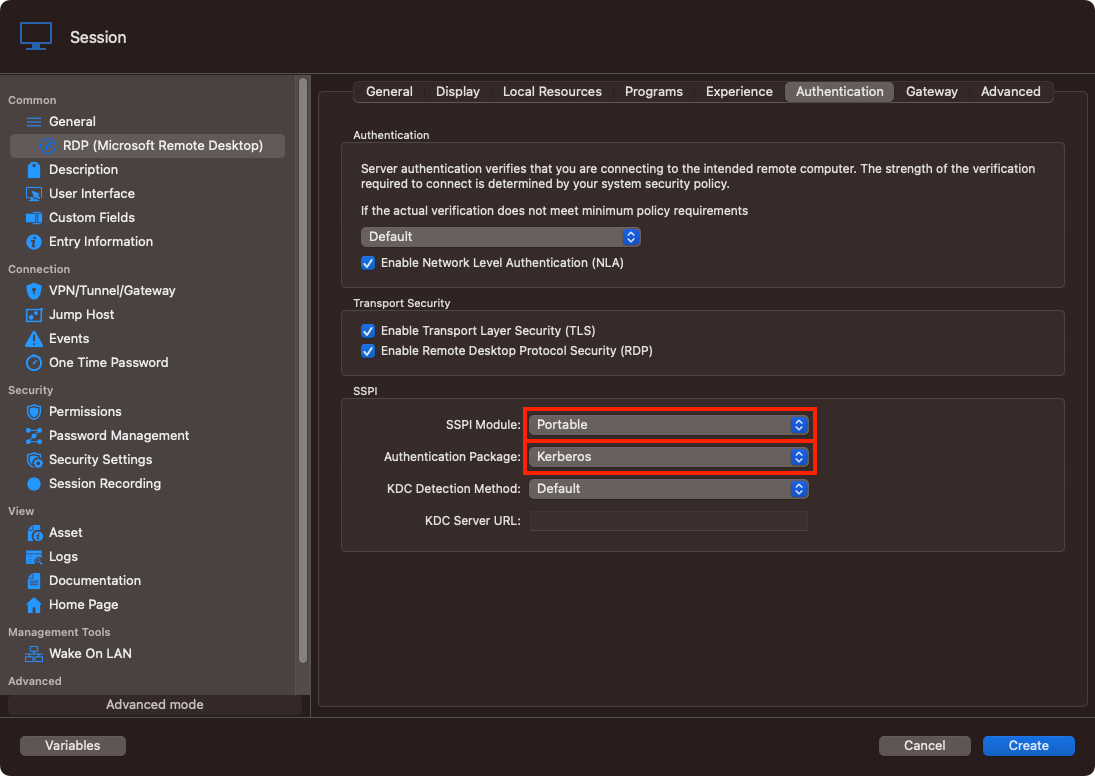
Best regards,
Xavier Fortin
ProtectedUsers.png
Thanks for not forgetting about it.
It's a pity, but I no longer have access to update the application.
Hi Xavier
Im using Windows 10 and RDM 2023.2.9.0. The setting you mention in your screenshot is not possible to use (always greyed out).
Do I need to configure something else first?
Is it possible to use this setting as well through Devolutions Gateway?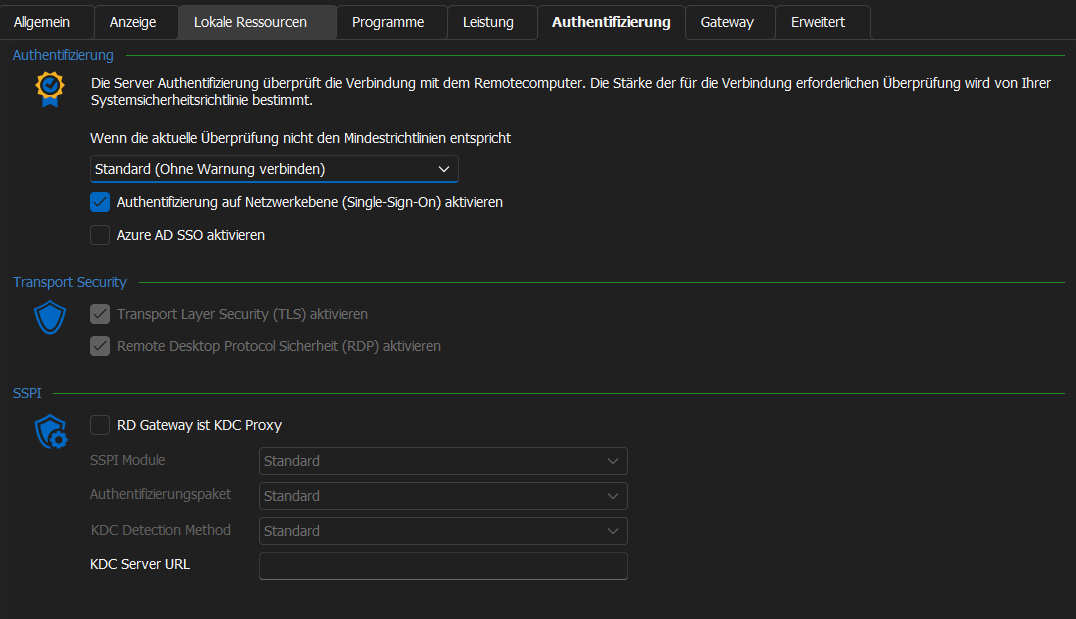
a5ee2f43-7f36-4f5b-b33e-f8a10dbff828.png
Hi Jannisroth
I see you're using RDM Windows, things are a little different in this case.
By default, RDM Windows using the Microsoft RDP client which can utilize the Microsoft APIs for kerberos authentication. Therefore, these settings are not available in the default configuration because they shouldn't be needed. Only if you switch to using the FreeRDP engine will you have the option of using the Devolutions authentication module.
So - using a "protected users" account under a Windows client should just work, however the feature relies on kerberos authentication and that has certain infrastructure requirements. If this is not working for you, I suggest posting a question in the Windows section of the forum.
Finally, this should all work via Devolutions Gateway. It's important to enable RDP API Hooking in Options > Types > Remote Desktop. Again, if you try this and it's not working in your environment I'd recommend posting a question on the Windows section of the forum so the proper staff will see it.
Please don't hesitate to post back if something isn't clear or you have further questions!
Kind regards
Richard Markievicz
