Users that aren't created can log in and see everything?!
Howdy,
So, we had a couple people install RDM yesterday but I hadn't yet created their User accounts inside of RDM. I asked them what happened when they logged in and they were able to get in and see everything and edit everything. This is a problem.
Is there something I have to set so that if people don't have a User ID within RDM, that they won't be able to log into the program? Otherwise anyone in our company could install it and start messing with things...
Thanks.
All Comments (8)
Hello,
What type of data source are they using?
Maurice
We use SQL for our Data Source.
Hello,
So your users already have access to the database through domain membership? What DB role are they into?
Have you created security groups to protect your sessions?
Maurice
We have security groups within RDM which I thought would make it so that if someone didn't have an ID created inside of RDM, that they wouldn't be able to see any sessions or anything but that doesn't appear to be the case.
RDM uses a service account in the background to access the database. The RDM Admin section is what we though twas controlling who could get to things.
Hello,
This is not how it works. Did you find documentation that was hinting at that? If so, we will fix it ASAP.
RDM uses the identity in the data source definition to identify the user and his permissions. Each user must use a unique set of credentials.
Allowing direct access to the DB is in fact frowned upon in the context of compliance with many regulations out there. That being said, the great majority of our community is comfortable with that and/or they do not need to be compliant with anything,
Our most secure system is by using Devolutions Server as a back end. Alternatively, you can control the credentials individually and redistribute locked data source definitions that people have no idea what their passwords are.
Best regards,
Maurice
I checked with our DBA and we looked around and it does appear that RDM is using the user's local account to access the DB. He thought it was using a Service Account but it doesn't appear to be that way.
So, what we do currently is I go into RDM | Administration | Users. I create a user and check the Integrated Security box and then find the user from our AD system.
Once I add them in, I then add them to a role/group depending on what department they are in. However, it appears that if someone tries to log in before I have created them a user, that it just bypasses the security groups and gives that person full access to everything?
I was assuming that if someone ran RDM but they did not have a User created, then they would obviously NOT be in any Roles or Groups so they then wouldn't be able to see any sessions.
Hello,
If you grant too high a level of permissions in SQL Server, you bypass our security. Lets follow the steps.
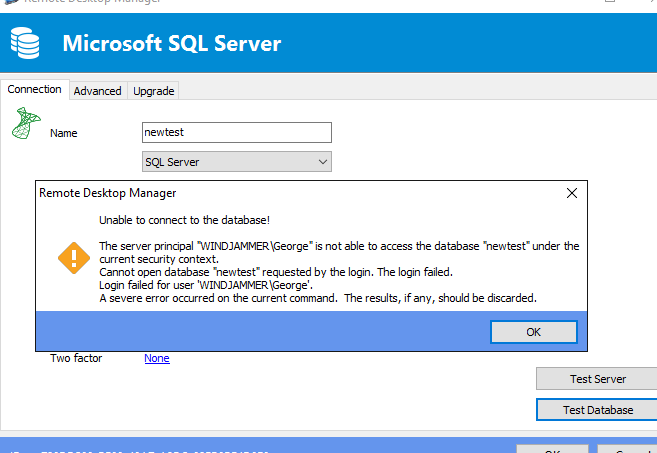
I create a new DB, then try to access it with a user in my domain. Fails with this...
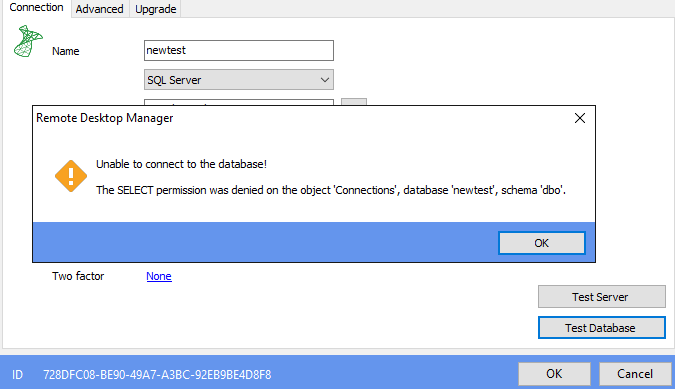
I go give that person access by giving the account the PUBLIC role, fails with this...
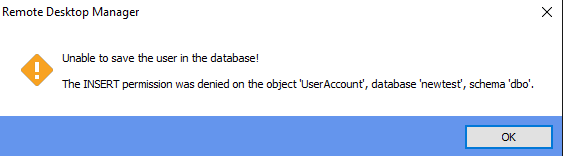
I then grant him the DATAREADER role, it allows me to register the data source, but when I log in I get this error....
Exactly what permissions are you granting these user?
Maurice
step3.png
step2.png
step1.png
OK, we think that the user who was testing this for us logged in with a Domain Admin account which granted him access to everything by default. We had someone else test it and they got denied right away when they tried to log in. So I think everything might be working properly. I'll have to check with the original person to see how he logged in.
Sorry for the confusion.