Roles get not assigned based on AAD group
Product: PowerShell Universal Version: 4.2.21
I have now tried (almost) everything - even complete re-install / re-configuration of Universal PowerShell with no change whatsoever.
I have a “normal” user-account and an admin-account. both are direct members of an ad-group “ssp-admins”. I have configured a role accordingly.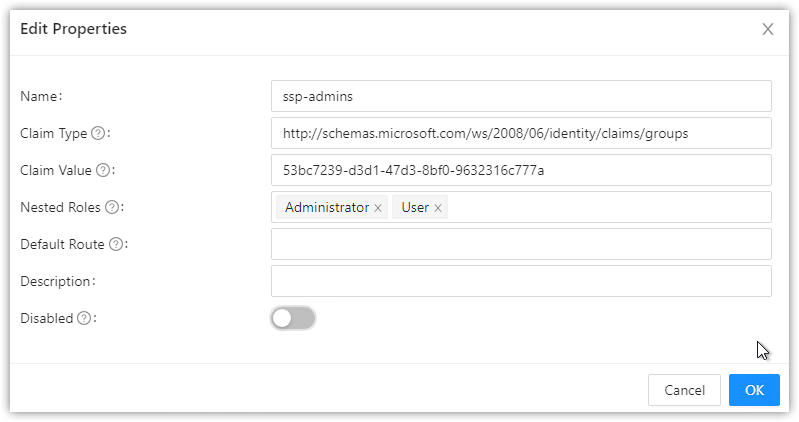
however - the page to show which roles are assigned only shows groups when I log in using the admin-account - but not when I use my “normal” user-account.
New-UDGrid -Container -ColumnSpacing 2 -Content {
New-UDGrid -Item -ExtraSmallSize 12 -SmallSize 12 -MediumSize 12 -LargeSize 12 -ExtraLargeSize 12 -Content {
New-UDTypography -Text 'welcome home'
}
foreach ($Role in $Roles) {
New-UDGrid -Item -ExtraSmallSize 12 -SmallSize 12 -MediumSize 12 -LargeSize 12 -ExtraLargeSize 12 -Content {
New-UDTypography -Text $Role
}
}
}
why is the role not assigned to my normal user account even if they are both members of that group?
KR
G.
PS: I have set up SAML2 (Azure AD) as authentication method
PPS: the behaviour does not change when removing all nested roles
dcc844b5d24de6c860be416c5c1a9220382e26a7.png
All Comments (2)
I also wonder how I could debug/log what happens when users log in? I could not find any information about this.
For testing purposes I now assigned the Administrator role manually to my “normal” user and clicked on View Claim Information only to see that no groups for that user are listed. This now explains why the role assignment does not work, but I still don’t understand why claims for those users are not listed/received by PSU.
I also double-checked with a colleague who has the same types of users (admin and normal) and it’s the same for those. Admin user has groups listed in claims, normal user does not.