Kerberos failure via Devolutions Gateway (KDC proxy) caused by duplicate UPN across forests
Kerberos failure via Devolutions Gateway (KDC proxy) caused by duplicate UPN across forests
Hi,
I wanted to post this on the forum in case someone runs into this in the future.
Without revealing them, thank you to the customer who found this.
The issue we had was related to Kerberos not working when using Devolutions Gateway as a KDC proxy in an environment where the client sits in Domain A but is trying to reach into Domain B. The Gateway is in Domain B.
Despite the configuration on the AD side being properly configured, we only got generic NTLM downgrades from the Remote Desktop Manager client and a generic "Account restriction" message.
Here’s what they figured out:
The issue was caused by having two users with the same "User logon name". Even though the users were in different domains (and forests), the duplicate UPN caused ambiguity during cross-forest Kerberos principal resolution. This interfered with Kerberos realm discovery, leading to Kerberos failing silently and falling back to NTLM, which ultimately resulted in the misleading:
“A user account restriction (for example, a time-of-day restriction) is preventing you from logging on.”
Once the duplicate user logon name was made unique across the environment, Kerberos authentication started working as expected through the Gateway.
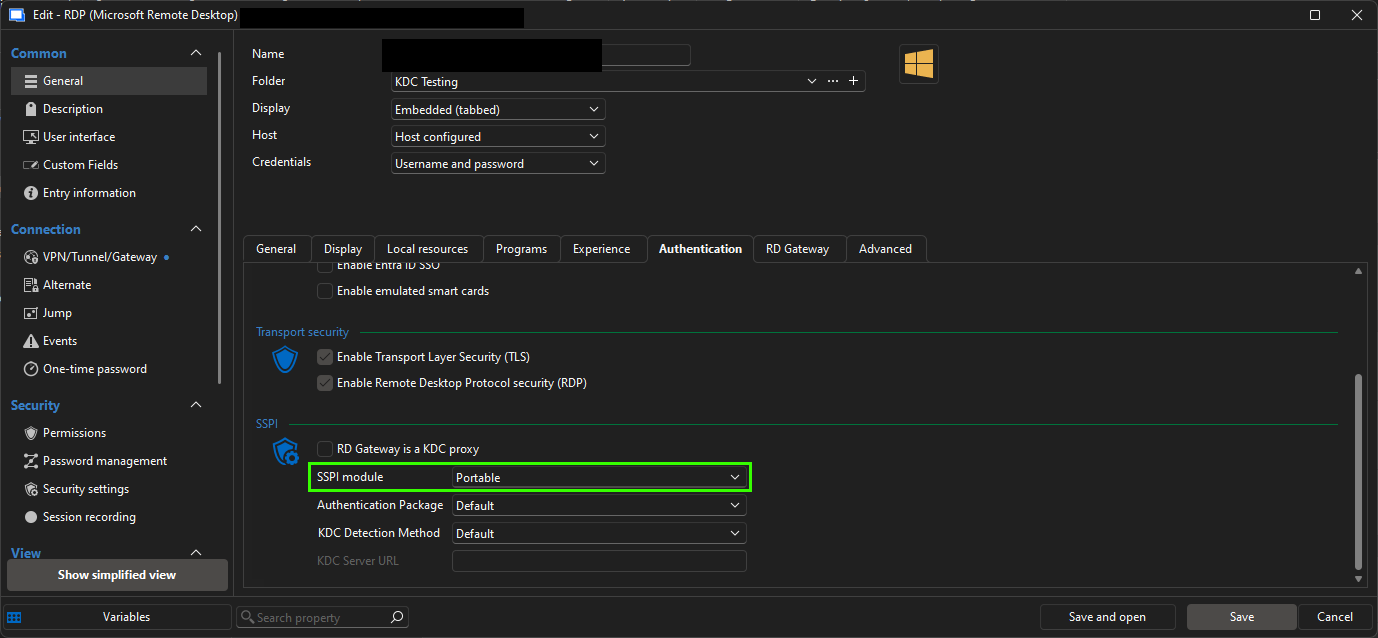
Before figuring this out, the workaround was to use FreeRDP with the SSPI module in portable version. This seemed to bypass the fallback lookup of the Kerberos realm that Microsoft RDP performs by default. Like so: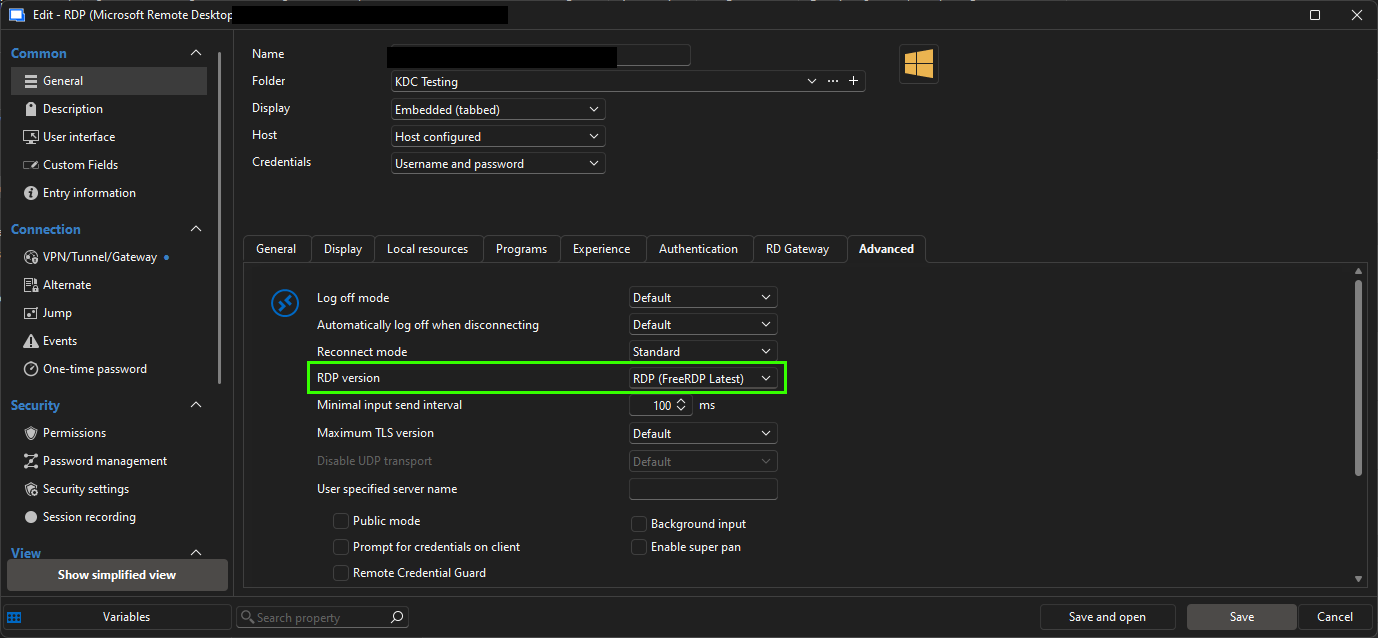
Hopefully this saves someone a few hours of troubleshooting.
Best regards,
Marc-Antoine Dubois
ead03bf5-da05-426d-a70d-e3f940927453.png
ce2cb1c0-6e44-45a7-92fe-2056b633c631.png