Multiple handle_https_peer failed errors
In our Devolutions Gateways logging we find a lot of errors, like
- HTTP server: error shutting down connection: Broken pipe (os error 32)
- HTTP server: peer closed connection without sending TLS close_notify
- TLS handshake failed: tls handshake eof
Logs:
2025-11-04T17:33:52.985760Z ERROR listener{port=7171}:https{client=172.16.1.43:60994}: devolutions_gateway::listener: handle_https_peer failed error="HTTP server: error shutting down connection: Broken pipe (os error 32)"
2025-11-04T17:34:13.184212Z ERROR listener{port=7171}:https{client=172.16.1.142:50816}: devolutions_gateway::listener: handle_https_peer failed error="HTTP server: peer closed connection without sending TLS close_notify: https://docs.rs/rustls/latest/rustls/manual/_03_howto/index.html#unexpected-eof"
2025-11-04T17:34:33.094822Z ERROR listener{port=7171}:https{client=172.16.1.142:50951}: devolutions_gateway::listener: handle_https_peer failed error="TLS handshake failed: tls handshake eof"
Is there something we can do to fix these errors?
We have 2 Linux VMs with Devolutions Gateway version 2025.3.2, also 2 Windows Servers with Devolutions Server 2025.3.4.0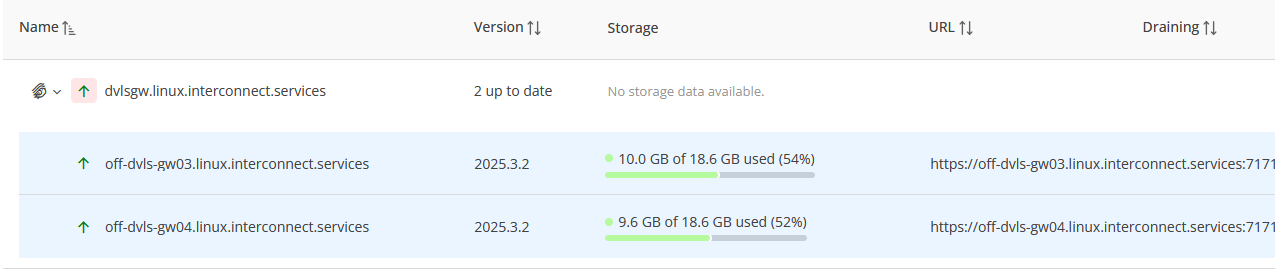
Config off-dvls-gw03:
root@off-dvls-gw03 devolutions-gateway # cat gateway.json
{
"Id": "3e95bdfe-99ba-41e4-96b6-1f755015935e",
"Hostname": "off-dvls-gw03.linux.interconnect.services",
"ProvisionerPublicKeyFile": "provisioner.pem",
"ProvisionerPrivateKeyFile": null,
"TlsCertificateFile": "server.crt",
"TlsPrivateKeyFile": "server.key",
"Listeners": [
{
"InternalUrl": "tcp://*:8181",
"ExternalUrl": "tcp://*:8181"
},
{
"InternalUrl": "https://*:7171",
"ExternalUrl": "https://*"
}
]
}
Config off-dvls-gw04:
root@off-dvls-gw04 devolutions-gateway # cat gateway.json
{
"Id": "f2bf2b4c-9011-434b-9c96-e88c5059f9fa",
"Hostname": "off-dvls-gw04.linux.interconnect.services",
"ProvisionerPublicKeyFile": "provisioner.pem",
"ProvisionerPrivateKeyFile": null,
"TlsCertificateFile": "server.crt",
"TlsPrivateKeyFile": "server.key",
"Listeners": [
{
"InternalUrl": "tcp://*:8181",
"ExternalUrl": "tcp://*:8181"
},
{
"InternalUrl": "https://*:7171",
"ExternalUrl": "https://*"
}
]
}afbeelding.png
All Comments (1)
Hi,
I reviewed the errors you’re seeing:
- Broken pipe (os error 32)
- peer closed connection without sending TLS close_notify
- TLS handshake failed: tls handshake eof
These typically happen when a client (or a probe) disconnects early, e.g., a browser tab closes, a load balancer health check doesn’t complete TLS, or a scanner opens and drops the connection. They’re noisy but benign and don’t indicate a server-side fault. Successful sessions should be unaffected.
Apart from these error logs, did you observe real connection failures?
What you can do to reduce noise:
- Ensure health checks on port 7171 perform an HTTPS/TLS check (not plain TCP) and complete the TLS handshake.
- Verify that no tools are hitting the HTTPS port with non-TLS traffic.
- If you’re using scanners/monitors, consider excluding the Gateway listener from those probes.
We’re also looking at reducing the log severity for these expected disconnects in a future update so they don’t appear as errors.
Best regards,
Benoit Cortier