PAM and Active Directory Tiering
Greetings, we are about to start a project where the customer is going to define a new Active Directory Tiering mode. I found the following article interesting and wanted to ask the feedback of the community about their recommendations and personal experiences with this matter:
https://www.riskinsight-wavestone.com/en/2022/10/security-bastion-pam-and-active-directory-tiering-mode-how-to-reconcile-the-two-paradigms/
Regards
All Comments (2)
Hi Mario,
Here's my two cents as an observer, I am not a practitioner. My focus is designing the best PAM for a reasonable amount of bucks.
The tiering model was deprecated by the new(ish) Enterprise Access Model, mostly in reaction to the explosion of the cloud and interconnected systems. Privileged Access Workstations (PAW) also became a factor at the same time.
picture below for the not faint of heart... you can still see 3 tiers if you squint, but with a few "complications" (ref Microsoft)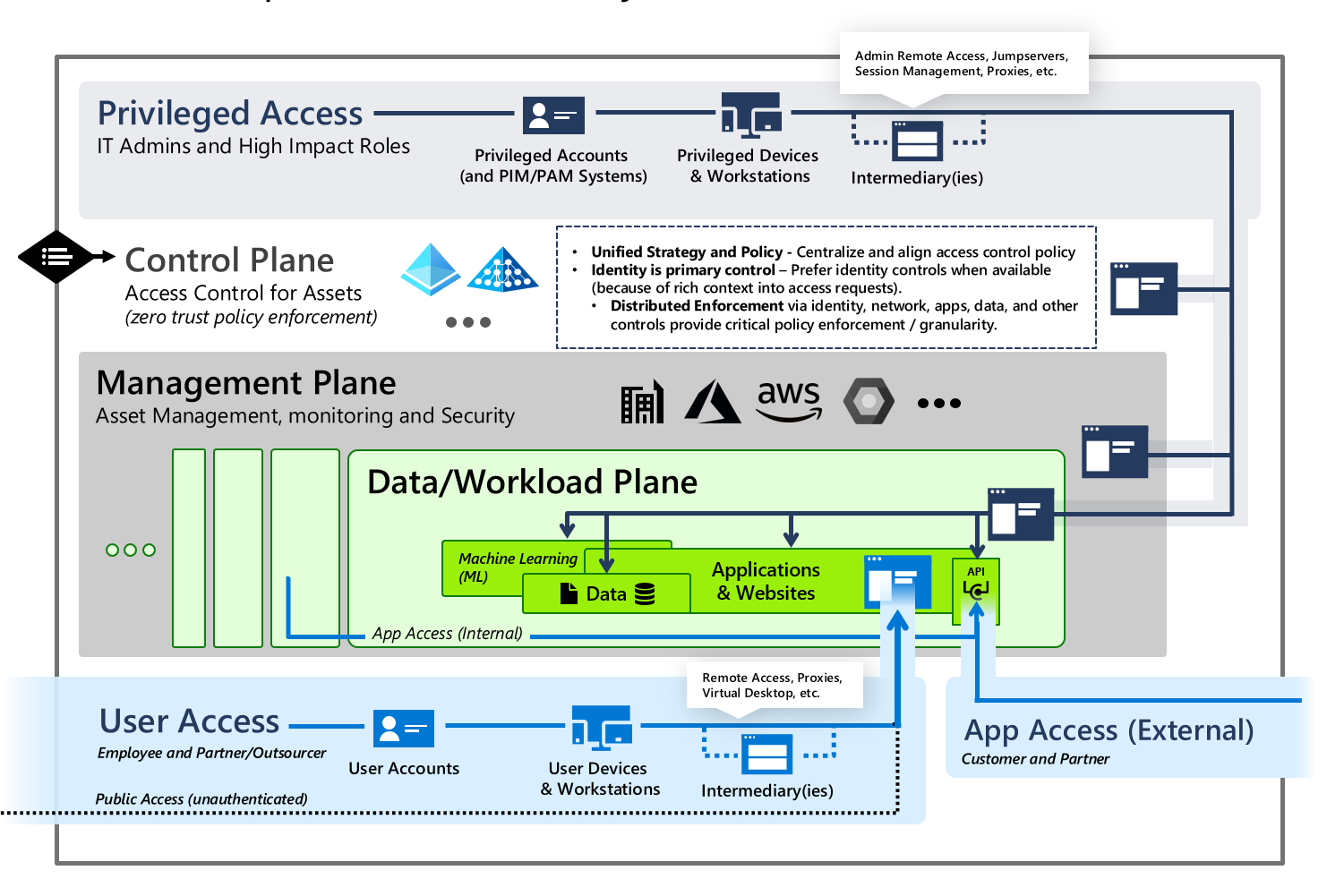
The reference you provided almost seems like an advert for our Gateway. I agree that you need at least one per tier, and you cannot understate the importance of the "watertight" aspect. At Devolutions, we use many gateways, and PAWs are looked into especially to manage T0. Lets remember that credentials and MFA are rendered unnecessary if the bad guys steal your authentication tokens. We feel its critical to not allow T0 tokens on T1 assets.
I'm anxious to see if other customers will get involved in this thread, but I will poke our internal IT/Security to get their thoughts.
Maurice
privileged-access-over-underlying-planes[1].png
Hi Mario,
To add to what Maurice said, a very important thing to get right if you plan to use PAM and bastion hosts to manage your T0 assets, is to make sure that those systems and their underlying infrastructure components are also included in said T0 and are managed accordingly.
For PAM specifically, it still makes sense for a tiered environment (even for the T0). The benefits it brings can complement those brought by enforcing the use of Privileged Access Workstations.
For bastion hosts, if we limit its definition to hardened hosts on which you RDP/SSH to further reach privileged assets, I would agree that in a scenario where you are already enforcing PAWs, they are probably redundant. On the other hand, if we extend their definition to include modern gateways born in the ZTNA era (like Devolutions Gateway ;)), they can still be relevant as they add an additional protection at the network layer and they can be more granular and convenient than traditional VPNs.
Simon Chalifoux