Bypass 2FA for certain IPs
0 vote
It would be an awesome feature to add the ability to bypass 2FA for allowed IP sources. For example, if my users are in one of our offices then I don't really need them to use 2FA. It's only if they are outside of our network that I want them to use 2FA.
Can you please consider adding an option where you can add a list of "safe" IP addresses and if the user is coming from that IP it bypasses 2FA?
All Comments (19)
Hello,
What kind of data source do you use for that?
Regards
David Hervieux
We're using DPS
Perfect,
I will forward you request to the DPS team.
Regards
David Hervieux
Hello,
I will add this to our product board. Sadly our slate is quite full for our September release. Most likely it would be done for the next version, but it concords with the introduction of "organizations" and stuff in that area, so we are further splitting Identification from Authentication, its a good fit..
Maurice
Thanks Maurice,
This is great news that it's not too far away. Without this ability we can't implement 2FA as it would just be too much of a daily burden for our staff.
Appreciate the priority and reply
Hello,
I will add this to our product board. Sadly our slate is quite full for our September release. Most likely it would be done for the next version, but it concords with the introduction of "organizations" and stuff in that area, so we are further splitting Identification from Authentication, its a good fit..
Any news on this Maurice?
Hello,
No news. We haven't gotten the organization piece yet.
We have discussed it at length though, our existing Whitelist/Blacklist mechanism of IP addresses will be reworked into Policies. Its close, but not started yet.
Best regards,
Maurice
Ok thanks for the update
Hi Maurice
Has there been any progress here? We are very very keen to implement 2FA due to the amount of people working from home during COVID but we need to be able to exclude people who are connecting from the office otherwise it will have too much of an impact.
Hello,
No progress, it cannot be implemented in our current release cycle. I hope to have it in 2021.2 which is planned for October.
Best regards.
Maurice
Hi Maurice
Is this still planned to be release in October?
Just so we're on the same page, here is an example of what Office 365 has for 2FA which works brilliantly
Hello,
Monday morning I would have answered yes, but we've been asked to push for an early September release date, at the cost of delaying certain features in minor builds over the months of October and November. I'm not able to commit to a specific build at this time, but the policy engine is critical for our 2022 roadmap.
For the design from Azure, I like it as well, I ask the team leader to look at it.
Best Regards,
Maurice
Thanks to sjames for suggesting this feature and Maurice and the DPS Product Team for working on this. My team is also very interested in this feature. While delegating the entire login process to an external provider (i.e., SAML) would be the easier route, we have a requirement that DPS be available even if our SAML provider (AAD/ADFS) were to go down. A built-in policy engine with 2FA rules including IP restrictions and bypasses would be the best solution for us.
Hello,
Monday morning I would have answered yes, but we've been asked to push for an early September release date, at the cost of delaying certain features in minor builds over the months of October and November. I'm not able to commit to a specific build at this time, but the policy engine is critical for our 2022 roadmap.
For the design from Azure, I like it as well, I ask the team leader to look at it.
Best Regards,
Hi Maurice,
Do you have an update on an ETA for this feature? MFA is pretty important to us but we simply can't implement until this feature arrives.
I'm hoping the Jan release of RDM 2022 will have it - or am I being too optimistic?
sadly no, priorities have shuffled and our authentication model was pushed up on top in order to remove front-end involvement in any security aspect.
we’ve pushed it to the 2022.2 release, it’s in the top of my personal feature list. I sincerely hope we can keep that on top.
Maurice
sadly no, priorities have shuffled and our authentication model was pushed up on top in order to remove front-end involvement in any security aspect.
we’ve pushed it to the 2022.2 release, it’s in the top of my personal feature list. I sincerely hope we can keep that on top.
That's a real shame as this is a big security hole for us, but it is what it is.
When is it anticipated that 2022.2 be released?
typically we start the beta cycle late Q2, so release is in Q3
Maurice
Bumping this feature request. It's one of the main pain-points that is keeping my users from replacing their existing tools with RDM/DPS.
Hello,
It is already possible to bypass 2FA based on IP in Devolutions Server. We forgot to add the information in this thread, sorry about that. You can configured a security policy (renamed to Conditional Access Policies in the next version 2023.2) to bypass 2FA based on different rules and one of those rules is the IP. Here is how you can configured a such rule :
1 - Go to Administration -> Server Settings -> Security Policies
2 - Select the target "MFA"
3 - Add a policy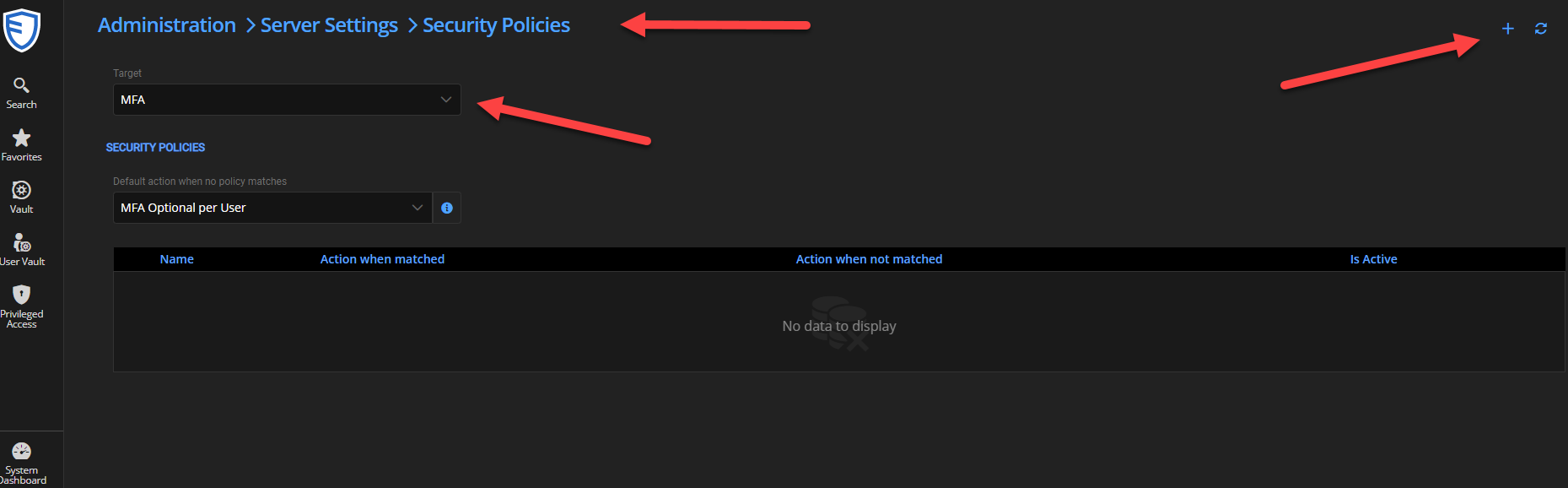
4 - Select the action to apply when there is a match or not
5 - Add a rule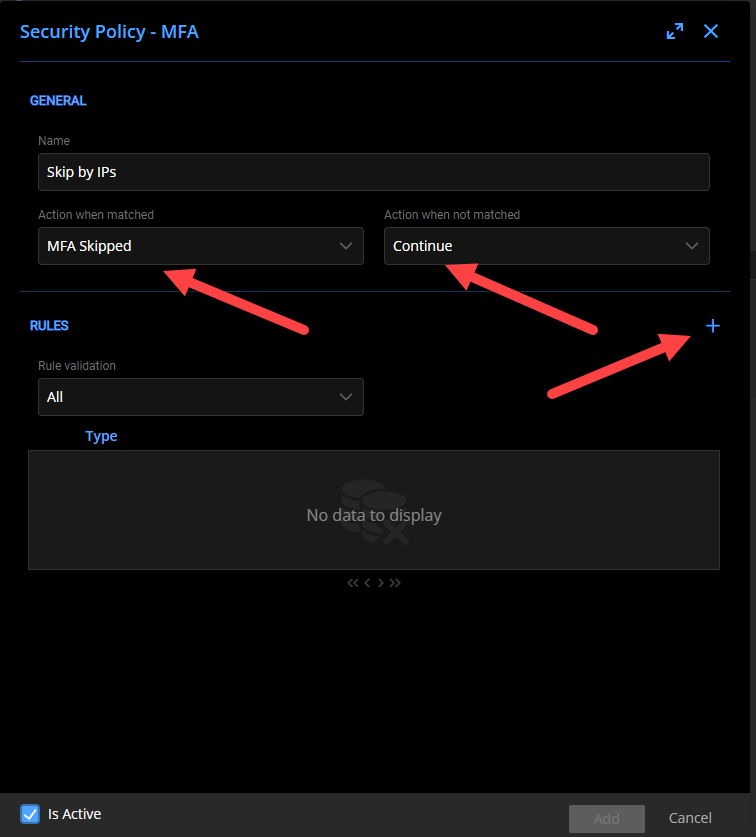
6 - The rule can be done on many conditions. One of those is the IP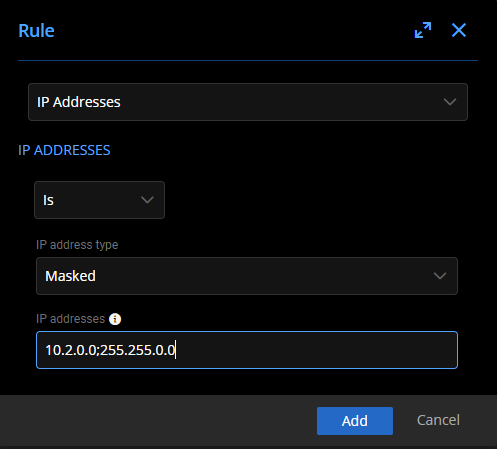
Let us know if you have more questions to configure that.
Best regards,
François Dubois
6bcf0414-a167-49a9-92e8-044706649091.png
f95aeae3-3b07-4255-bd2c-06fb665d86c7.png
ca65a39f-116f-4d8f-b523-94665a1a5c37.png